-
Notifications
You must be signed in to change notification settings - Fork 48
New issue
Have a question about this project? Sign up for a free GitHub account to open an issue and contact its maintainers and the community.
By clicking “Sign up for GitHub”, you agree to our terms of service and privacy statement. We’ll occasionally send you account related emails.
Already on GitHub? Sign in to your account
Recent Mass AV False Positives #54
Comments
|
I’m aware of the situation and I’m trying to get to the bottom of what’s going on here. |
|
Just to clarify, are you seeing these false positives with old versions of the application? |
|
@CloneTrooper1019 Decompiling it and looking through the C# code didn't point to anything suspicious imo, but I'm not sure what extent of the program could be modified, for example, I have no idea if it's possible to insert assembly code into the application that wouldn't get decompiled. |
|
Excerpt from https://malwarefixes.com/threats/trojanwin32-occamy-c/:
Hope this provides some help analyzing the issues. Seems like Windows Defender labels anything that accesses Windows preferences is a trojan? |
|
With that said, several other antivirus programs are still reporting it as such. |
|
@Hexcede Would you say that it's safe to download and disregard Windows Defender? |
Yes, I would say so. We are able to view the source code of RobloxStudioModManager since it's a .NET application (it's compiled to non-native bytecode which is what allows it to run on several platforms as well as 64/32 bit machines) using a ton of decompilers. I've had a look myself, and I don't see anything out of the ordinary. This, however, does not mean there isn't a possibility the file has been infected through an attack. I've investigated the source code a bit further, and I believe that what is being detected is actually the fact that RobloxStudioModManager both downloads, and launches Roblox (lol). Essentially what happens when RBXModManager starts up is it contacts Roblox to locate versions, test branches, etc. This behaviour, since it happens without any user input, is probably seen as being "backdoor-like." There are plenty of ways to get Windows to execute an arbitrary program like this at launch, so my guess is that Windows defender and other AVs see this as a threat since it's contacting a remote service, downloading files, and other things. #58 This was resolved! 😄 |
|
Looks like it’s being false flagged again. |
Yep, and it looks like Windows Defender isn't the only thing detecting this either. A lot of engines are falsely detecting this for some reason. Edit: And it looks like even super old versions are also being flagged |
|
Could it be Windows Defender? Because whenever I try to extract it, it just deletes itself, tried making non-exe, it successfully extracted, but as soon as I renamed its extension to exe, it just deleted itself. |
Yes a lot of AV engines are detecting this right now. (Again) |
|
UPDATE & ???: Windows defender now flags the RSMM executable (and even very very old releases) even more aggressively and this makes it impossible to download the source as a zip in chrome currently. Norton and many other AV engines all flag RSMM with pretty high confidence. This is extremely strange and I have no clue what is causing RSMM to be flagged on such a massive scale and I'm beginning to wonder if RSMM is perhaps being targeted for/by something. I've submitted RSMM to a few AV engines so far and have not gotten much yet. I'm gonna ask about this on the devforum. This is sounding more serious I think. |
|
So the conclusion so far from the devforum post is as follows:
(Currently the latest release results in 40 flags, which I expect is due to the pdb debug path in the executable for some weird reason) |
|
Applied this patch. This seems to have reduced it significantly. |
|
@CloneTrooper1019 Crab rave |
|
This effectively means that Kaspersky and ZoneAlarm are the only false positives remaining and they classify RSMM as "non virus adware" which is very obviously not the case. |
|
This issue is occurring again since the latest release, and Windows AV keeps flagging & deleting mod manager. Disabling "Real-time Protection" doesn't work either. I've "allowed" the program to remain on this PC, but if I restart Windows it seems to forget and requires me to reinstall mod manager and re-allow the file to remain. |
|
Try whitelisting it @Mullets-Gavin |
|
I found what line's cause the detection by Microsoft defender RegistryKey robloxPlaceCmd = robloxPlace.GetSubKey("shell", "open", "command");
robloxPlaceCmd.SetValue(_, $"\"{modManagerPath}\" -task EditFile -localPlaceFile \"%1\"");and RegistryKey studioUrlCmd = GetSubKey(robloxStudioUrl, "shell", "open", "command");
studioUrlCmd.SetValue(_, modManagerPath + " %1");Both inside of the With both of these lines the virustotal score is It may be a good idea to try and make the program not use the registry, this should reduce the false positive count by a significant amount. |
|
@GlowingUmbreon Sure but would that really be an end-all catch for this? When I tried building the program as a debug version instead, virus-total dropped a large chunk of its detection count as well because the resulting code was not similar enough to be detected by the existing database, only for it to ramp back up again shortly after. There is nothing inherently wrong with the registry key changes I'm making, Roblox Studio does a similar amount of registry key changes and it isn't marked as a virus. The key issue is that the program runs RobloxStudioBeta.exe after downloading and extracting it from Amazon S3. While the program is not acting malicious, it exhibits the behavior of a trojan and has no other choice but to assume it's unsafe. I might have to just fork up like $300-$500 a year to have the application signed by a certificate authority, which I can afford to do but it's really annoying that I even have to. |
|
@CloneTrooper1019 While this will not fix all cases this would fix windows defender according to virus-total, which I feel most of the false positives come from since its built into windows, which is a step in the right direction. |
|
I rescanned the file on virus total and the amount of detections dropped from 39 (10 months ago) to 27 so the false flags have improved but still a lot of AVs detect it. |
|
Got a new one: I don't believe signing it will help a lot; from what I can see antivirus vendors don't really consider a signed executable safe anymore since there's been a resurgence in malware that has been signed. It's definitely a factor in their conclusion but it's not a bulletproof solution. The best way of resolving these would to be manually contact each provider and get it whitelisted, but this takes time and it would have to be done for every release. A possible solution would be to have the downloading functionality in a separate worker executable, and then get that worker to be cleared by AV companies. As long as it isn't updated, in theory it should be fine. Just make sure it's included as part of the download instead of it being downloaded by RSMM. |
|
Bitdefender silently blocks this, creating an exception does absolutely nothing. I would suggest prioritizing av's that silently block it without exceptions. |
|
Technically, this has never been fixed. The issue was closed because there's a workaround, however it requires admin privilages |
|
I hope avast stops detecting it soon |
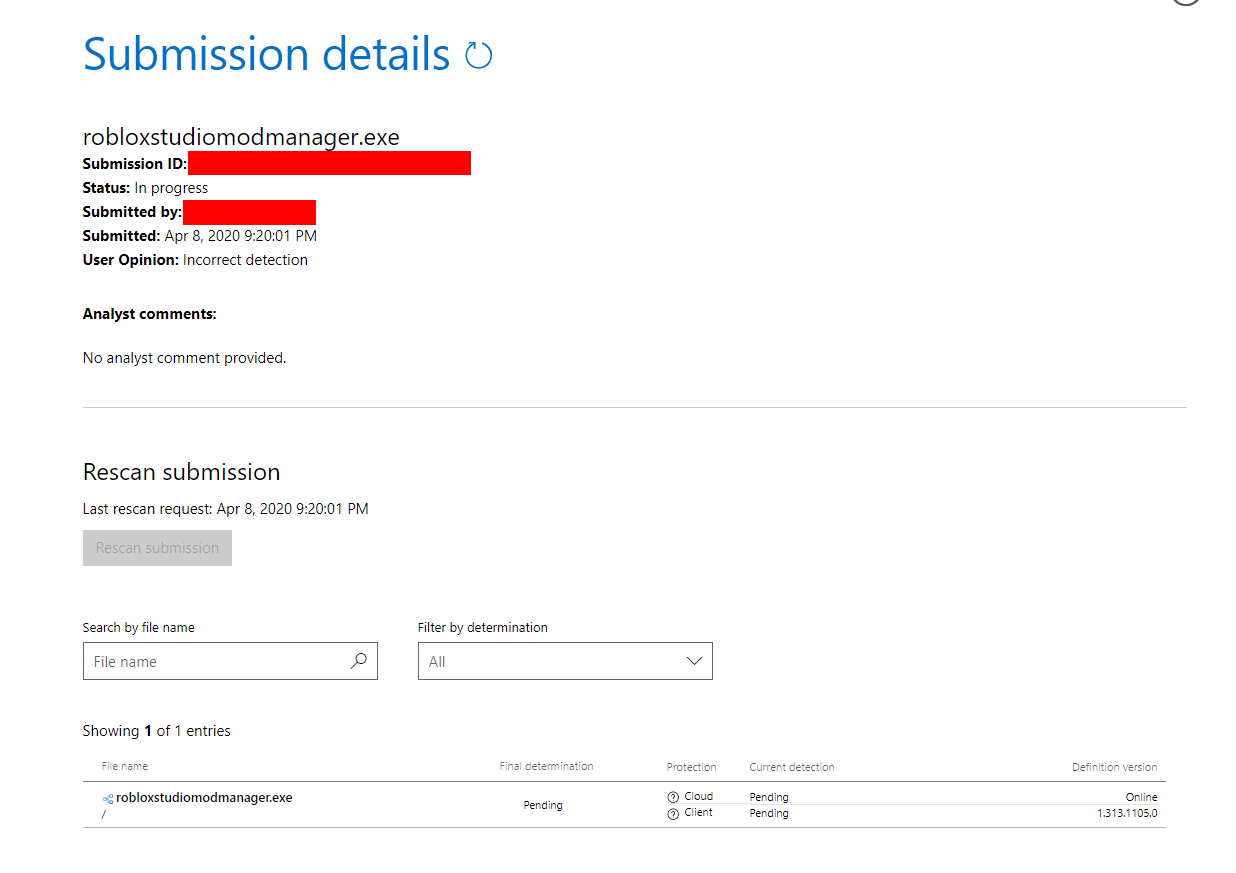






Windows defender now falsely detects RobloxStudioModManager as a trojan virus, as shown below.

Additionally, as you can see in the following VT scan, a lot of anti virus softwares are flagging this.
https://www.virustotal.com/gui/file/e0b3bce3d68eaf6d049c724d95c03788ba11e062868c3a4761f08fd6caa9fd01/details
I am not sure what would or could have triggered a false flag. This serves as both a heads up to users visiting, as well as a notification to the developer of this tool. Thankfully, since RobloxStudioModManager is a .NET executable, manual analysis is fairly easy to do. From what I've looked at, I don't see anything malicious doing a fairly thorough search of the compiled file.
For some reason, despite showing up in decompiled code, there is a marked inclusion of the string "C:\Windows\system32\cmd.exe" within the program may have potentially flagged antivirus software. VirusTotal marks this as a "highlighted" item, and interestingly it does not seem this is present in the code. A potential fix could simply be to use "cmd" if it is present and I simply missed it since System32 is part of the path by default on all Windows machines (and removing it from path will cause mass issues for any program using the command line).
Additionally, it seems that false flagging of RobloxStudioModManager has been an issue previously unfortunately. Hopefully this isn't a large problem.
The text was updated successfully, but these errors were encountered: